What is FSMO Roles and Steps To Transfer FSMO Roles
What are FSMO roles i.e. Flexible Single Master Operations
It is one of the best interview question that Interviewers ask in the interviews. After reading this article you can answer the question i.e. “What is FSMO Roles“. Flexible Single Master Operation (FSMO Roles) is a feature of Microsoft’s Active Directory.
Now the question arises:
What FSMO roles do?
What are FSMO Roles best practices?
How to transfer and seize Flexible Single Master Operation Roles?
What are the command line to check them and transfer them to another Domain Controller in Active Director?
Keep reading this article to get detailed information about all those questions.
There are total five types of FSMO roles in Active Directory i.e. Domain Naming Master, Schema Master, Primary Domain Controller (PDC), Relative Identifier Master (RID master) and Infrastructure Master. By default, all five roles are assigned to the first DC (Domain Controller) created in the forest. However, you can transfer or distribute them to other DC.
Forest-wide FSMO Roles
Schema Master Role (SM)
Since, schema master is forest-wide role it means there will be only one DC having schema master in a forest. It contains all the information about the attributes and classes of the forest. DC having Schema master should be online while modifying the schema. It is advised that we should not modify schema unless and until it is very essential. Schema modifies automatically when we install Exchange Server.
Domain Naming Master Role (DNM)
It is also a forest wide role which means that by default the first Domain Controller of the forest has Domain Naming Master. This FSMO role is required while adding a new domain in a forest or while removing an existing domain from a forest. The DC having DNM should be online while performing these operations. Don’t get confused between adding or removing domain in/from a forest and promoting or demoting a DC in a domain. Domain Naming Master is not required while performing promotion or demotion of an Additional Domain Controller.
Domain-wide FSMO roles are
PDC Emulator Role
Primary domain controller (PDC) is a domain-wide FSMO role which means first Domain Controller of each domain of a forest have this role. PDC is required to sync time between all the DCs and also between Domain Controller and other computers of a domain. It also records all the password changes from client computers and replicate/update to all the DCs throughout the domain. It is one of the most important roles because of its time sync feature, it should be online 24×7. Domain users would not login to member servers or client computers if PDC FSMO Role is not available.
RID Master Role
All objects in a domain have unique ID known as RID. Relative Identifier Master role (RID role) provides the pool of RID’s to each of the Domain Controllers in a domain. When a DC creates a user, group, or computer object, a unique RID is assigned to each object. If DC having the RID is not available then none of the DC is able to renew its RID pool. The RID in Active Directory provides a pool of 500 unique RIDs to each DC and renews their pools when 250 unique IDs remains left. DC can create about 500 objects even if the RID FSMO Role is not available.
Infrastructure Master Role
Infrastructure Master provides all the group membership updates from one domain to another domain. This FSMO role is not required in an environment is of single domain. Infrastructure role is required in the environment of a forest having multiple domains. It is advised not to have Global Catalog and Infrastructure on the same Domain Controller because it have partial information of other domain and therefore, it doesn’t allow full updates of other domains.
How to transfer FSMO roles through command prompt in Windows Server 2012 R2
1. Consider a scenario of two DCs. Here, we have two Domain Controller i.e. DC01 and DC02 in a forest. In this post, we are transferring FSMO roles from DC01 to DC02 using command prompt.
2. What is the command to check FSMO roles ?
Another good interview question is, what’s the command to check FSMO Roles? To check FSMO roles from command, run the command “netdom query fsmo“. Open command prompt and type “netdom query fsmo“. Here, we can see that all the five operation masters are on DC01 because DC01 is the first DC of our forest.
3. To transfer FSMO roles open command prompt (either on DC01 or DC02 as an Administrator) and type “ntdsutil” command. Ntdsutil command is used for database management of Active Directory Domain Services, it is very critical command for many administrative tasks.
NTDSUTIL command is not only limited to get detailed information about Flexible Single Master Operations roles but it is an Active Directory tool required for many other functions, which we’ll explain later in detail. NTDSutil command is also used to transfer these roles.
Then type “roles” for activating FSMO maintenance.
Type “connections” and then type “Connect to server DC02” to establish a connection to DC02 using the credentials of locally logged on user. In this command, DC02 is a name of that server on which we have to transfer FSMO roles.
4. Now, type “q” to exit from server connection. Type command “transfer rid master” to transfer RID Master role and hit enter. Now Role Transfer Confirmation Dialog Box appears regarding the confirmation of the transfer.
Click on Yes to continue. It will transfer the RID to DC02. Similarly you can transfer all of them. If you are not sure about the exact command to run then type “?” and hit enter for help.
Type “transfer domain naming master” to transfer Domain Name Master Role and similarly type the name of role that you want to transfer.
5. Now, we will verify that the transfer of RID is successful or not. Again type “netdom query fsmo“, now we can see that RID is successfully moved to DC02.
Note: If you want to transfer all of them, then use “transfer rid master” command and replace the RID master with the name of the role which you want to transfer.
How to transfer FSMO roles through GUI in Windows Server 2012 R2
1. In this example, we will transfer FSMO roles from DC01 to DC02 through GUI. For transferring PDC, we have to open AD users and computers of DC02. Either we can open AD users and computers directly from DC02 or remotely from DC01. To open AD Users and Computers of DC02 remotely, open AD users and computers on DC01 and then right click on AD Users and Computers[DC01.ITIngredients.com] and then click on “Change Domain Controller”.
2. On “Change Directory Server” select the DC to which you want to transfer the role. Here, we have selected DC02.ITIngredients.com and then click on ok.
3. Right click on Domain (ITIngredients.com) and then click on “Operation Masters” to transfer the FSMO roles.
4. From here, we can transfer only RID, PDC, and Infrastructure master. Click on PDC tab, here we can see the Domain Controller currently owning this role and the Domain Controller to which we have to transfer PDC. Click on Change to transfer the role.
A Dialog box appears regarding the confirmation of transfer the PDC, click on yes to confirm and accept.
5. ADDS Dialog box appears regarding the acknowledgment of successful transfer of PDC operation master.
6. Open command prompt and type “netdom query fsmo” to verify if PDC is transferred to DC02 or not.
How to transfer Domain naming master and Schema master through GUI in Windows Server 2012 R2
Besides command we can also use GUI i.e. Active Directory Domains and Trust to transfer Domain Naming Master to another Server.
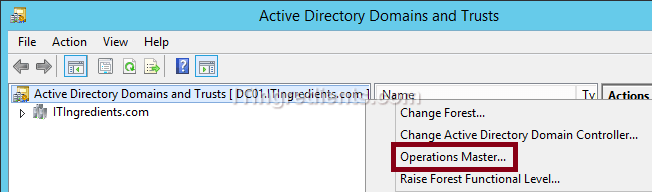
1. Click on Start and then down arrow to open Active Directory Domain and Trusts. Right click on “Active Directory Domain and Trusts [DC01.ITIngredients.com]” and then click on Operation Masters.
2. On “Operations Master console“, we can see the significance of DNM, the current owner of this role and the name of server to which it can be transferred. Click on “Change” to transfer the ownership.
3. To change Schema Master from GUI, we have to open MMC console by typing “MMC” on the run.
4. Click on File then “Add/Remove Snap-in” to add console of schema master.
5. On Add/Remove Snap-ins console, we will not be able to see the Active Directory Schema in Available Snap-in. Cancel the snap-in.
6. Open Run and type “regsvr32 schmmgmt.dll“, it will register the “Schmmgmt.dll” file and add the Active Directory Schema in Add/Remove Snap-ins option of the MMC console.
7. A dialog box appears regarding the success of regsvr32 schmmgmt.dll.
8. Now again open MMC console and click on the file then Add\remove snap-in. Select “Active Directory Schema” and click on Add. Click on OK.
9. Now right click on Active Directory Schema [DC01.ITIngredients.com] and then click on “Change Active Directory Domain Controller” to open the console of DC02.ITIngredients.com.
10. On Change Directory Server console select DC02.ITIngredients.com and click on OK to continue.
11. Right click on “Active Directory Schema [dc02.itingredients.com]” and then click on Operations Master.
12. On “Change Schema Master“, we can see the relevance of Schema master that it manages the modifications to the schema and only one server in the forest can own Schema master. We can also verify the current owner of Schema Master and can transfer it from this console if required.
How to Seize FSMO Roles
We learned the steps to transfer FSMO roles through GUI and Command Prompt. Now the question arises, what if the current holder of any Operation Master crashes?
In this situation, we cannot safe and gracefully transfer any role to another server because the current holder cannot be contacted. For this, we have to seize them from the current holder to an existing server. We cannot seize any them through GUI. It can only be performed through command prompt.
In this example, we have assumed that DC01, the current holder of PDC is crashed (we disconnected the server from network) and now we have to transfer PDC to DC02 but the transfer is not possible due to the unavailability of DC01.
So, in this scenario we’ll seize PDC and not transfer it. We’ll again use Ntdsutil command to seize the roles.
1. Open command prompt and type “ntdsutil” and then “roles“.
Type “connections” and then type “connect to server DC02“. Here, DC02 is the name of that server which will be the new owner of PDC after seizing. Type “q” to exit from server connection and then type “seize PDC”.
2. Seizure confirmation dialog box appears regarding the confirmation of the seize of PDC. Click on YES to continue.

3. Firstly, it will attempt for safe transfer of PDC FSMO role before seize. The safe transfer will not be possible because the current holder of the PDC is crashed or not available. Now the server would proceed to seize the PDC when safe transfer fails.
2. Now, we’ll run “netdom query fsmo” command on command prompt to verify the success of the sieze of PDC FSMO role. We verified that now DC02.ITIngredients.com is the new holder of PDC. It clearly shows that seize of PDC is successfully completed.
Conclusion:
In your organization you can either have all the FSMO roles on one Domain Controller or you can transfer FSMO roles to other Domain Controllers, depending on the size of your Organization. If you have multiple Domain Controllers then I would recommend to distribute them to other Domain Controllers. It prevents the situation of single point of failure. In case of disaster it would not impact the entire Organization.


























